Students
CCT Research Students
Ibrahim Alam
artificial intelligence, software engineering, algorithm optimization

Ruba Alsmadi
cybersecurity, privacy, digital forensics

Peyton Andras
cybersecurity, machine learning, neuromorphic computing
Babangida Bappah
program analysis, memory forensics, binary analysis

Bibhushita Baral
artificial intelligence
Sideeq Bello
user and measurement studies of privacy, security, and safety
Matiwos Birbo
adversarial machine learning, privacy-preserving machine learning, AI

Christopher Bowen
reverse engineering, memory forensics, malware analysis
Lauren Bristol
digital forensics, vulnerability analysis, AI security
Colton Bruni
molten salt electrochemistry, nuclear fuel cycles, nano-optics

Jacques Comeaux
type theory, compilers, asynchronous circuits

Matheus Costa
software engineering, HCI, VR

Dalton Diez
neuromorphic computing, artificial intelligence, algorithm design

Daniel Donze
memory forensics, red teaming, artificial intelligence
Aidan Eiler
ICS/OT security, machine learning & AI, digital twinning

Christian Facundus
memory forensics

Taha Gharaibeh
memory forensics

Ronald Gibson
malware and exploit development, vulnerability analysis

Sam Goodwin
file carving, digital forensics
Ahmad Hadi
3D data processing, robotics, vision-language-action systems

George Hendricks
digital forensics, file carving

Sam Hildebrand
artificial intelligence, software vulnerability testing, industrial control systems security
Linta Islam
CS education, human-computer interaction
Eric Jones
hardware hacking, electrical engineering

Marcellina Kazigati
industrial control systems, artificial intelligence, threat intelligence

Mst Eshita Khatun
cybersecurity, user privacy, LLM
Chloe Kinsley
software development, large language models
Erich C Kruger
code vulnerability detection, artificial intelligence

Brandon Lara
compilers, exploit development, reverse engineering
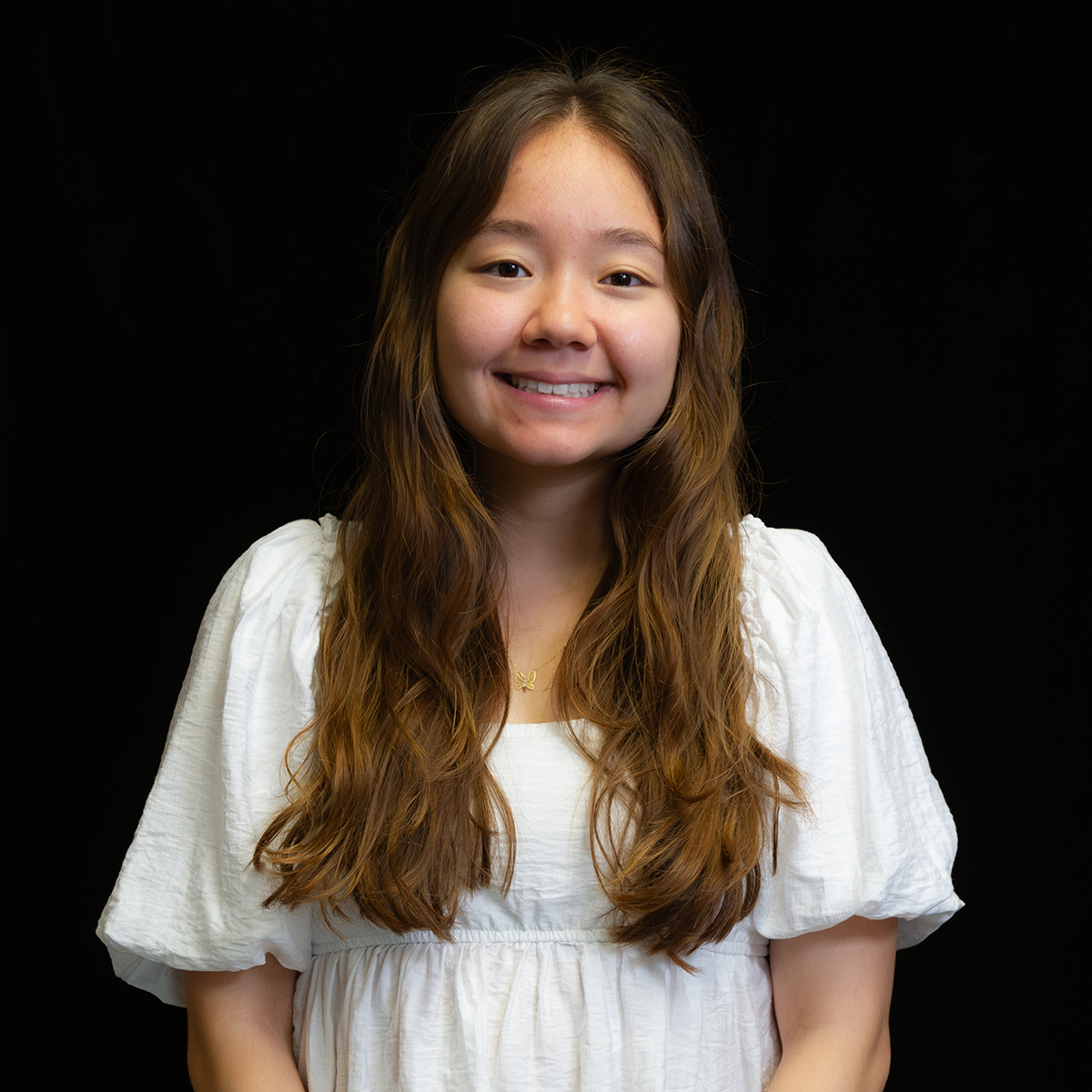
Kim Nguyen
privacy analysis, mobile applications, artificial intelligence
Nurjahan Nipa
security and privacy, vulnerability management, machine learning
Aidan O'Donnell
artificial intelligence, nuclear nonproliferation

Lauren Pace
malware analysis, memory forensics
Catherine Rodriquez
neuromorphic computing, artificial intelligence, large language models

Tyler Saizan
digital forensics, file carving

Koosha Sharifani
ML security, adversarial attack
Maxwell Shroyer
artificial intelligence, large language models, software development

Trevor Spinosa
tba
Zhiyong Sui
malware analysis, artificial intelligence

Karley Waguespack
digital forensics, file carving
Justin Woodring
quantum security, artificial intelligence